In today’s digital landscape, driving traffic to websites and online platforms is crucial for success. Many website owners and online marketers employ various strategies to…
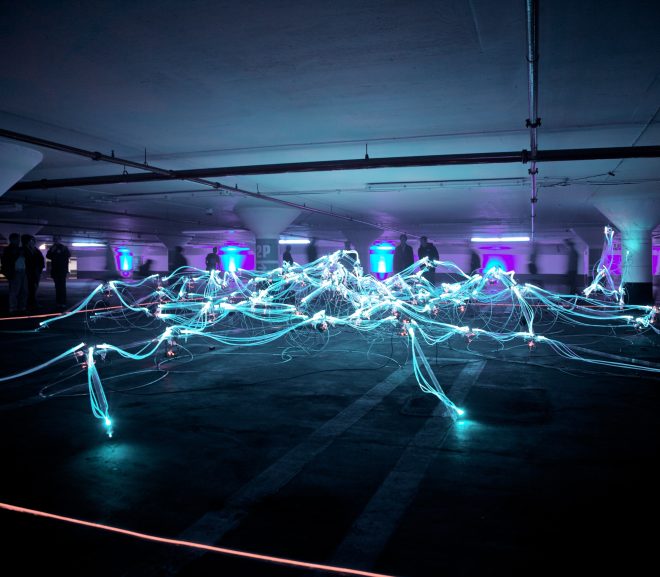
In the world of technology, the digital twin is a term that has been gaining massive popularity. But what exactly is it? Is it some…
WhatsApp is set to revolutionize its platform with the introduction of Channels, a feature that enables users to engage with social media-like content while safeguarding…
Summer can be the best time of year for fun in the sun, but it can also bring some serious heat. When temperatures soar, it’s…
Summer is officially here, and what better way to spend those sunny days than with a good book? Whether you’re lounging on the beach or…
Whether you’re an Instagram enthusiast or an occasional user, chances are you’ve found yourself wanting to view someone’s Instagram story without them knowing. However, Instagram…
Summer is finally here! The season of sunshine, beaches, and relaxing outdoor activities. However, with all the fun that summer brings, it’s important to remember…
Are you tired of playing multiplayer games and feeling disconnected from your teammates? Do you wish there was a way to communicate with them in…
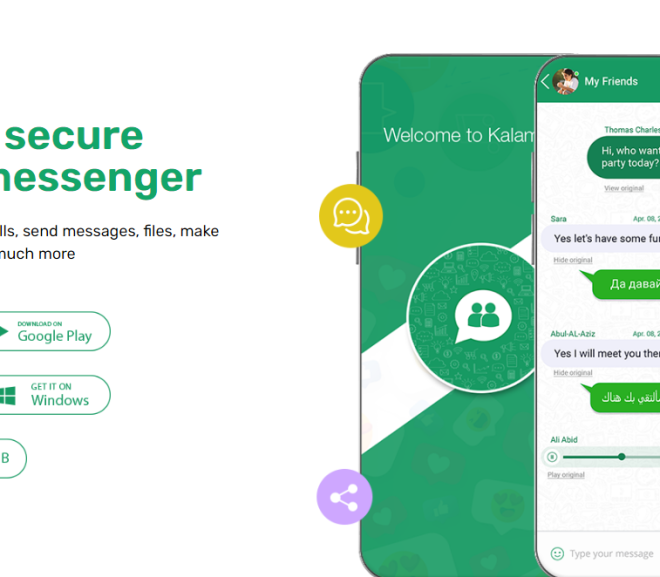
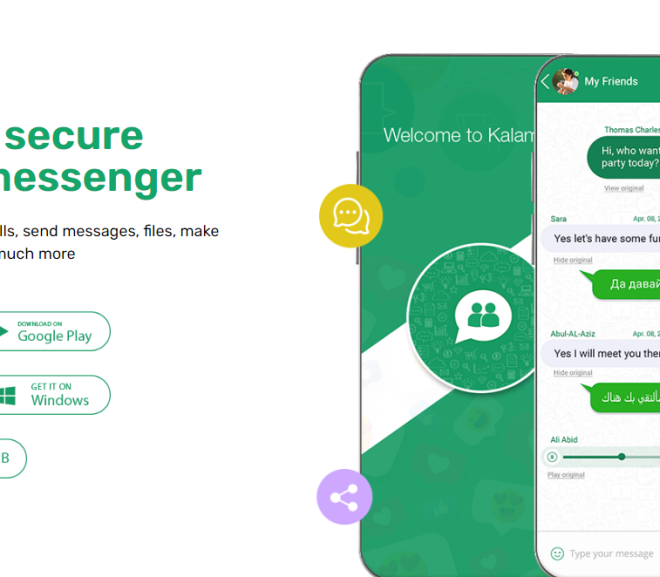
In today’s digital age, instant messaging has become an integral part of our daily communication. From simple chats with friends to business meetings, we use…
Sharing snippets of our lives through Instagram stories has become the norm for many of us. Yet, there are times when we wish to revisit…